Source routing is basically an option in IP (layer 3) where a packet can instruct a gateway (for example the sonciwall) which hops to send the packet to. Its like the client deciding which route the packets should take. Now this of course is kinda bad because if the client (let’s say he’s a hacker) decides on the path, then he can route all traffic to some listening box, doing all sorts of stuff to the traffic passing through it.
It also means that the hacker can make an attack seem as if its originating from another PC, or even “bounce” an attack. For example, lets say yo have a business CompanyA, which is very well protected. But CompanyA is partners with CompanyB and they have VPNs running to and from each other. CompanyB is not very well protected. If a hacker compromises CompanyB, he / she can use source routed packets to attack CompanyA by traversing through CompanyB… nasty huh?
So , its not good having the source routed packets, that’s why we drop them…
FYI… the IP header of a source routed packet include the desired routing hops like so:

Note the “loose source route” and our gateway (10.71.10.254) specified in the packet
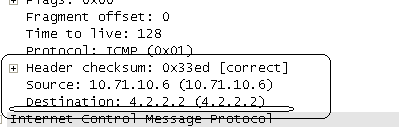
Compare this to a normal packet:
You see no loose routing and the destination is directly 4.2.2.2
Also FYI, source generated packets can easily be generated using the ping –j command
ping –j [next hop list] target
For example I used ping –j 10.71.10.254 4.2.2.2 to create all the above traffic.
More information for the ping command in microsoft from here : http://technet.microsoft.com/en-us/library/bb490968.aspx
You would get no response to these packets because our gateway drops them for security