Please note: this software has only been officially tested on Ubuntu and CentOS distributions. The VPN software uses community based vpnc software, please direct support questions about the actual client to your distribution’s support channels.
The following documentation is based on Ubuntu 12.04 LTS
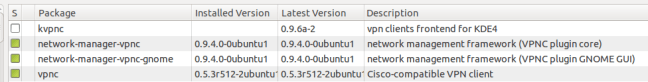
– Install the following packages on your system:
* network-manager-vpnc
* network-manager-vpnc-gnome
* vpnc
The above mentioned packages are all available via synaptic package manager:
– Right click on the network manager icon on the top right corner of the screen and select the “Networks Settings” option
– Click the + icon to add a new connection.
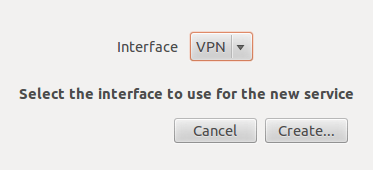
– Select the VPN interface type and click on create
– Choose the cisco compatible vpn option
– Enter the following details:
An appropriate connection name
Gateway: public IP of the GlobalProtect Portal
User: username
Password: password
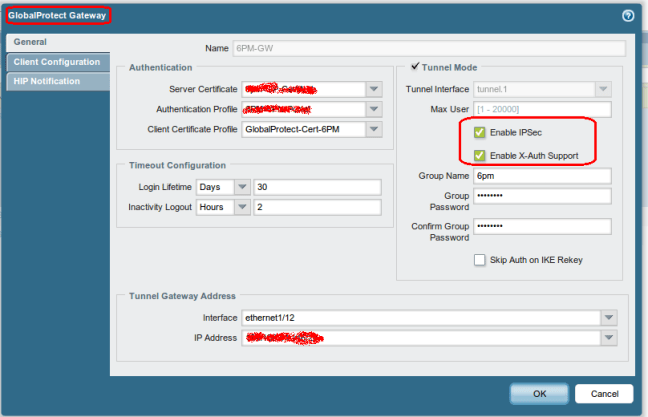
For the following two settings, you need to enable IPSec and XAUTH on the Palo Alto Gateway settings for this to be enabled, as can be seen below (Network > GlobalProtect > Gateways)
Group Name: group name
Group Password: password
The VPN will now be available as an option when clicking on the network manager icon. Once the option is selected, the network manager icon will turn into a padlock, indicating a successful connection
Known Issues and troubleshooting tips
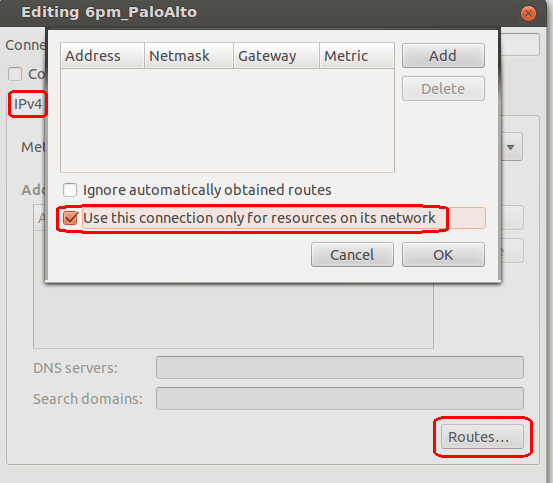
- By default the VPN client tunnels all traffic through the firewall. This is not under the firewall administrator’s control, and is purely a client issue. We have allowed internet browsing through the VPN tunnel, but you may notice a marked increase in your browsing latency. The client does allow you to “split-tunnel” and send only the required routes through the tunnel. This can be done by editing the properties of the VPN connection, browsing to the IPv4 tab and selecting the routes button. Make sure to select the option Use this connection only for resources on it’s network. You may also need to enter the routes manually in the table.
- You may notice periodic disconnects or loss of connectivity. This seems to be due to a bug in current VPNC versions that have issues with rekeying. Research on google should turn up some suggestions
- Generally all errors and debug messages are logged to /var/log/syslog. Check this location if you run into problems.


Hi. Thanks for the posting! It actually helped me out when I was setting up a vpnc connection to a Palo Alto unit I’m demoing.
I just want to make one comment. When you mentioned about the “known issues and troubleshooting tips”, you said that “By default the VPN client tunnels all traffic through the firewall. This is not under the firewall administrator’s control, and is purely a client issue. ” I have to disagree, because I don’t get this issue when using the vpnc client against a Cisco 2911 vpn. The spilt-tunnel policy works by default without any manual intervention on the client.
I only seem to experience this with the Palo Alto (PA-2050). I’m actually going to reach out to the sales engineer to see if he can better explain, but if I find out anything useful I’ll come back and post.
thanks again!
David
Excellent pls let me know if you find anything!
Thanks
Thanks a million it took me while to get GlobalProtect setup for my users. I thought fixing it for my personal Linux devices were going to be a pain but once it is built following this was way simple.
Thanks for posting. Worked like a charm.