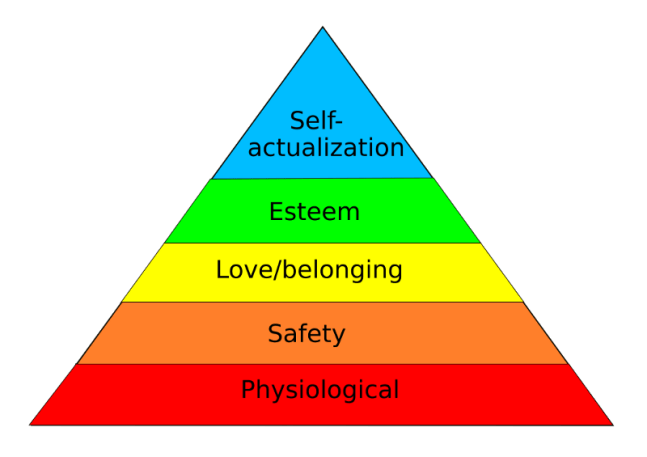
Many of us are probably familiar with the concept of the “hierarchy of needs”. The concept is usually depicted as a pyramid with humans’ more essential needs — such as bodily function — at the bottom, with more non-essential but rewarding needs towards the top:
What if we extend this concept of a hierarchy of needs into cyber security? It would help business owners and risk management teams asses how to approach implementing a holistic approach to protecting their business. Matt Swann went ahead and did just that. Here is his version of the cyber security hierarchy of needs:
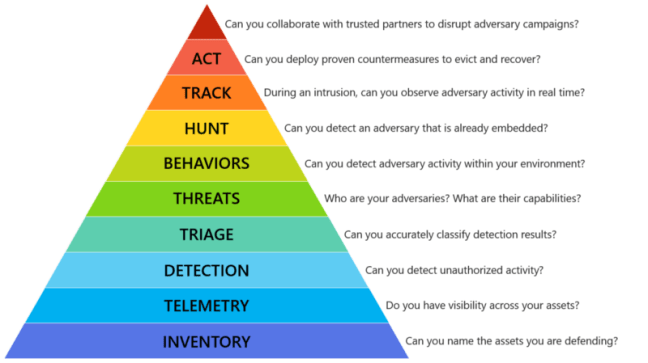
I believe it’s an excellent prioritization strategy to follow — but I probably can’t name a handful of organizations that I’ve worked with or for who implement more than the first two layers properly.
With enough discipline and automation in place, it is possible to achieve the first two basic layers successfully. Even basic actions like running periodic scans in your network or using centralized host provisioning help in this aspect. Simple NMAP scans will help you answer “Can you name the assets you are defending?”, while provisioning tools like SCCM, Chef or Puppet can ensure that telemetry agents are installed on all your assets, feeding data into a central location.
The next layer “Detection” is where things get interesting. How confident are you in your organization’s ability to “detect unauthorized activity”? A recent article from business insider reveals that only 21% of financial services institutions can answer this question confidently:

Another striking observation made from the above chart:
40% of respondents think they “have robust and fully automated” systems in place, but from those only about half of the respondents trust these systems to detect a breach. Even if you are in the minority of companies that have countermeasures in place, businesses seem not to trust these countermeasures very much — and we’re still on just the third layer of needs for an effective security strategy — seven more layers to go.
One theory to explain this observation is that most systems out there today rely solely on signatures and rules. If your adversary uses different attacks to those you have rules for, they can slip past undetected. On the other hand, systems based solely on anomalies are known to have difficulty coping with false positives, and with false positives already a problem in signature based systems (“Squealing” anyone?) we’re left with the thought that clearly, as an industry, security providers are failing at the hierarchy of needs.
Like most other problems, I believe that the best approach is a balanced approach. We should leverage the strengths of both signature-based and anomaly-based systems to cancel each other’s weaknesses. Anomaly-based systems can detect novel attacks that signature based systems cannot, while the latter can help reduce the amount of false positives by providing additional context to alerts (you would be much more likely to consider an anomaly as interesting if the IP address involved has just triggered a “scanning” signature rule). This is approach is the one we have decided to adopt here at CyberSift, with some very promising results.
While effective tools and Intrusion Detection Systems are just one piece of the puzzle, a properly designed IDS will help an organization define effective security practices and response plans that all together are the basis of tackling the security hierarchy of needs appropriately…
Catch Matt Swann’s original content here:
https://github.com/swannman/ircapabilities
Interested in learning more? Follow us on twitter or get in contact with us!
CyberSift – Security made intelligent. A hybrid IDS which leverages both signature & anomaly data mining techniques to simply cybersecurity

