In this article we’ll explain how to encrypt traffic going to an HTTP handler in NiFi, which is then forwarded to a backend HTTP server – in other words, an SSL offloading reverse proxy. Encrypting traffic in transit to NiFi involves the following steps:
- Creating a keystore containing a CA certificate
- Creating a truststore, which contains the above CA certificate
- Configure NiFi to use the CA certificate and truststore
Tips:
- Throughout this document we generate our own certificates using a GUI tool called “KeyStore Explorer”, which you can download from here: https://keystore-explorer.org/downloads.html
- If you already have certificates generated by your own internal CA, the UI tool will allow you to import the certificate
KeyStore Explorer is just a UI wrapper around the Java keytool command
Creating a keystore containing a CA certificate
Using KeyStoreExplorer, create a new keystore of type”JKS”. Subsequently:
Within KeyStore Explorer, right click and “Generate Key Pair” to create a new certificate or import an existing certificate to use as your Certificate Authority.
Once created, save a copy of this keystore (file > save as) and place it in a folder on the NiFi server
Creating a truststore, which contains the above CA certificate
A truststore allows an application (in this case NiFi) to determine if a client certificate should be trusted or not. This is typically used for client side TLS authentication (elasticsearch beats use this model for example) In our case, any certificate signed by the CA should be trusted.
In order to create a trust store, we must first export the CA certificate we just created above. To do so, right click on the certificate an export the certificate chain:
Ensure that PEM is selected and save the certificate:
Transfer the file to a directory in the NiFi server as before.
Open a command prompt as root and issue the following commands:
cd <directory_containing_certs>
keytool -import -v -trustcacerts -alias <insert_alias> -file <insert_correct_filename>.cer -keystore truststore.tsConfigure NiFi to use the CA certificate and truststore
At this point we should have both the keystore and a truststore in the directory. Configure NiFi to listen for traffic and accept only encrypted traffic by using the HandleHTTPRequest processor:
Configure the processor as follows:
All values can remain as per default, except for “port”, which should be configured to a sane port number, creating a default HTTP Context Map, and the “SSL Context Service”, for which you can select “Create new service…” from the drop down, which will show the following:
Everything can be left as per default, and click on “create”. This will create the ssl context service which you can configure by clicking on the small arrow beside it:
Once you click on the cogwheel to the right, you will be presented with a configuration screen to input the details of your keystore and truststore that we created in the preceding steps:
At this point NiFi is correctly configured to accept encrypted traffic
Putting it in a flow
The full template can be downloaded from here. The template would result in something like this:
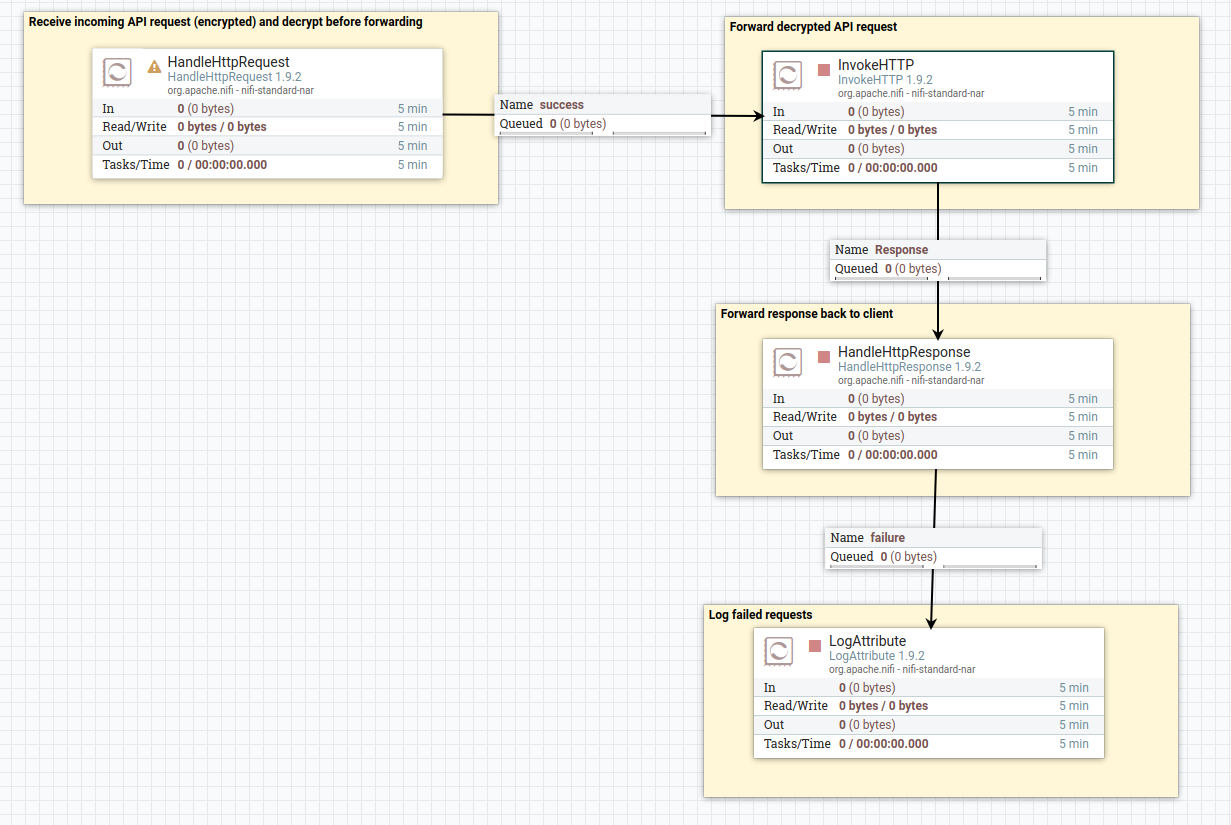
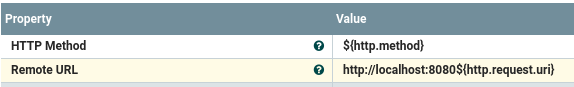
Note the use of “HandleHttpRequest” to receive the original (encrypted) request from the client, “InvokeHTTP” to forward the unencrypted request to the web server, and finally “HandleHttpResponse” to send the response right back to the client. Within InvokeHTTP., note the use of the NiFi expression language to forward the original client request to the target server properly:

You must be logged in to post a comment.