Microsoft has been migrating most of Azure’s functionality to the “Microsoft Graph API”, which is fantastic as that allows us to automate a bunch of things within the Azure cloud. However, the Graph API is secured behind an OAuth2 flow, and if you’ve ever dealt with OAuth2 you’d know that it revolves around “tokens” which are issued by a central authentication/authorization server for any given resource requested by the user. For those of you not so familiar with OAuth, you’ve definitely come across the “Authorize This App?” page of a number of web applications, where you’re asked to sign in and allow access to certain resources for an app you’ve enabled. That’s OAuth!

The problem is that these kind of flows assume there’s an end-user in the loop… i.e. someone who will click on the “allow” button for your app.
What if your app is a console app?
So what if your operating environment is not a desktop, but a server with only a console? This seems to be what some guides I’ve found are targeted at. For example, the below is an excellent post:
https://keathmilligan.net/automate-your-work-with-msgraph-and-python
And it gets you almost all the way there, but there’s still a bummer:
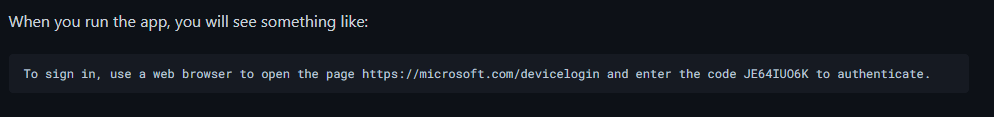
Ideally we’d love to avoid having the end user having to manually copy/paste this sort of thing
Nomenclature and daemons
After a bunch of searching I hope to save you, it turns out that there is a way of doing this, in what Microsoft terms “daemon console applications”, and they very helpfully provide a sample python script:
https://github.com/Azure-Samples/ms-identity-python-daemon/tree/master/1-Call-MsGraph-WithSecret
And that’s it! Rather than requesting a user token, the “daemon console application” uses an “app password” to generate a token and access the Graph API without bothering the end user.


You must be logged in to post a comment.