I hope this is an easier approach than several guides there are on the net. In this article, I’ll basically use part of a guide from the ubuntu server documentation to build a very basic but empty LDAP structure, and fill in this structure using the LDAP GUI tool called Apache Directory studio.
Apache Directory Studio is freely available from here
— The basic LDAP server is installed. The following commands were taken from the ubuntu server guide. Below are simply the commands needed (blatantly copied from the link provided…. more detailed explanation there):
- Install server:
sudo apt-get install slapd ldap-utils
- Install the appropriate schemas which describe object attributes and object classes:
sudo ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/ldap/schema/cosine.ldif sudo ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/ldap/schema/nis.ldif sudo ldapadd -Y EXTERNAL -H ldapi:/// -f /etc/ldap/schema/inetorgperson.ldif
- Build a very basic LDAP structure including the root of the domain and a user “admin”. In this example the domain is called “minty.local”. So the below text was placed in a file backend.minty.local.ldif
###########################
Note that the bold and underlined lines should be changed to whatever you are using, especially the domain and the “secret” password. Make a note of these entries, we’ll need them later.
- Add the above file to the LDAP database:
sudo ldapadd -Y EXTERNAL -H ldapi:/// -f backend.minty.local.ldif
- Add the admin account to the LDAP database (change the bold/underlined) by creating the file (/tmp/frontend.minty.local.ldif):
# Create top-level object in domain dn: dc=minty,dc=local objectClass: top objectClass: dcObject objectclass: organization o: Organization description: LDAP Root # Admin user. dn: cn=admin,dc=minty,dc=local objectClass: simpleSecurityObject objectClass: organizationalRole cn: admin description: LDAP administrator userPassword: secret
Once the file is created, add it using the command:
sudo ldapadd -x -D cn=admin,dc=minty,dc=local -W -f /etc/frontend.minty.local.ldif
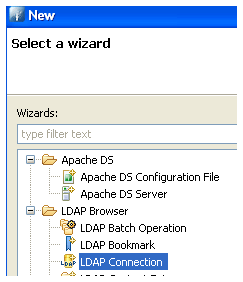
— At this point ready to use Apache Directory Studio. Open File > New > LDAP Connection
- Type in arbitrary name for the connection and server IP
- Select simple authentication, and enter the admin / password as entered in backend file: cn=admin,dc=minty,dc=local. Check authentication, this should worl
- Untick “get base DNs” and ented the DC components eg: dc=minty,dc=local
- You should now be presented with basic tree.
Note the object classes for container “cn” and “ou”. For example the below screenshot shows that OU has objectClass “organizatinalUnit”:
Adding an OU:
– Right click, new entry
– Select “Create entry from scratch”
– As an Object classes select an appropriate one, in this case “organizationalUnit”
– As DN, select “ou” and add name

– Click on finish and you should have a new ou.
Add new user to the OU
– As before, right click, select a new entry and start from scratch
– Select Object class “Person”

– As an RDN [relative distinguished name] Select “cn” and enter the user name
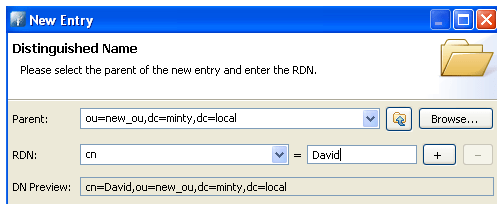
– Add “sn” (surname) and finish.
– Add an attribute eg password: Right click and select “New Attribute”

– Select Attribute type : userPassword, and finish
– Enter new password as SHA
Note that you may need to add object classes and attributes. For example, it is usally better to use the inetOrgPerson as object class rather than the “Person” object class as I did above
Some common object classes:
– Linux User : posixAccount
– Linux Group : posixGroup
– Microsoft User : inetOrgPerson / organizationalPerson
– Microsoft Group : group
I would really recommend connecting Directory Studio to an existing Active Directory ldap server and snooping around there to get a better understanding of LDAP classes and attributes.