While researching the best way to implement the SSL certificate monitoring feature for our Tutela product, we ran across the excellent Certificate Transparency Project. The project aims to “watch the watchers”, and provide independent certificate logs to monitor Certificate Authorities. Unfortunately for us, the project API endpoints do not return an easy-to-parse data feed. Instead, the logs contain base-64 binary encoded data representations of the certificates detected.
We won’t go into detail on how to parse this data structure from scratch, because there is some excellent material on the web on how to do this already. Instead, we were lucky enough that the official Google tools related to this project are written in Golang, the same language we use internally. The Google Github repository containing the code can be found here:
https://github.com/google/certificate-transparency
A quick look around that repository shows you Google are showcasing everything that’s possible with this project (rightly so – that’s part of good documentation). However, what if you are looking for only a small subset of the data returned (as was our use case)? We needed to dumb-down the toolset provided by Google, so as a quick proof of concept we set out to see if we could write a Golang utility which had a single goal:
“Given a start and end index, output the Subject of a certificate (i.e. which domain the certificate was assigned to)”
The below is the result:
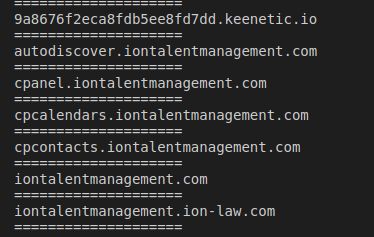
Building and running the above will return all domains which had a certificate issued to it starting from index 218772510 and ending with index 218772520.
Note:
- Note that in lines 13-14 we explicitly imported the tls and x509 packages under different names from the certificate-transparency-go repo (ctTls and ctX509 respectively). This has to be done since these two packages are also defined in the “crypto” golang package, but are slightly different to cater for differences in parsing packages. To avoid namespace collision this step is important
- The function getCerts defined in lines 28-45 is straightforward… it simply retrieves the raw certificate data from the JSON API, using types defined in lines 18-25
- The main work happens in the testSslCertMonitor in lines 47-92. This has been distilled from Google’s code, but essentially you can see a loop which grabs 20 certificates at a time (the max allowed is about 31), and depending on the type of data returned, parsing the binary data into the previously defined types before printing out the subject domain name
Hopefully this gist would make it easier to fit this excellent repo into your own codes and projects 🙂


You must be logged in to post a comment.